ISG Federal Solution
Your Agency Must Migrate
to Post-Quantum Cryptography

Take the First Step to Protect Sensitive Data and Ensure Compliance
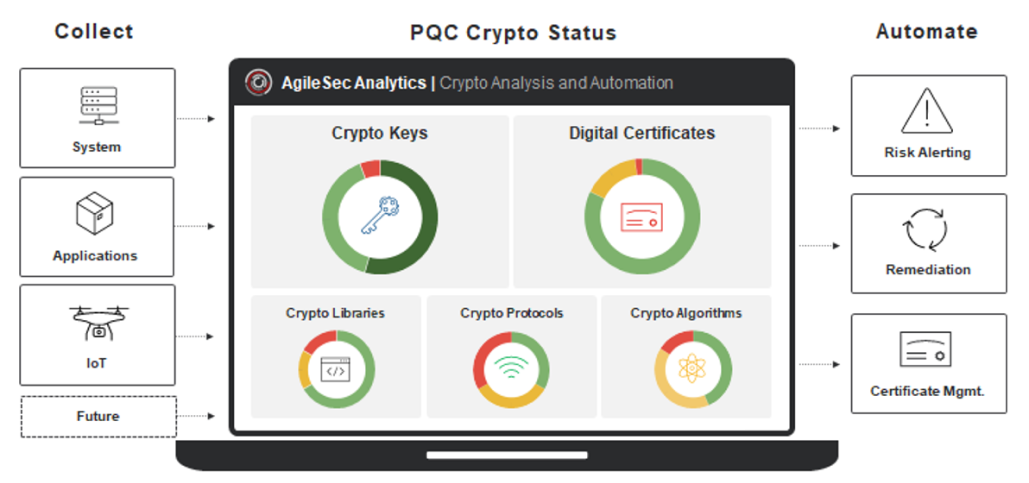
ISG Federal is a cryptographic security company that specializes in providing next generation cryptographic discovery, agility, and management solutions from the silicon firmware up through end-point applications. Our secure software enables the management and agility of all cryptographic assets across a digital ecosystem, enabling government agencies to automate and orchestrate cryptography usage.
Achieve Cryptography Visibility and Control – Quickly and Easily
Agency-appointed migration leads are entrusted to take immediate action to protect their agencies against the risks of a post-quantum world. Not knowing what cryptographic libraries are in use could have you in active risk. OMB memo M-23-02 issues clear guidance with an actionable timeline for migration leads to follow in order to rapidly understand and demonstrate the status of all of the cryptographic libraries in the enterprise and prepare for a post-quantum world.
ISG Federal’s lightweight, automated solution identifies cryptographic libraries without needing deep domain knowledge in either cryptography or the applications that contain them. With ISG Federal, you can:
Visualize your cryptographic dependencies and unknown vulnerabilities
Develop and deploy cryptographic policies
Automate and orchestrate a cryptographically agile ecosystem
Take the First Step:
Inventory Cryptographic Assets by May 2023
Meet OMB memo M-23-02 requirements timeline
Discover and analyze all of your cryptographic assets using the industry’s most comprehensive discovery and analysis tool for uncovering vulnerabilities and assessing threat criticality across digital certificates, keys, and encryption. With this initial step, you will be on your way to automating continuous monitoring and reporting of all of your cryptographic assets on a yearly basis and achieving comprehensive visibility, remediation, and control with crypto-agility.
Why ISG Federal?
Technical Experience and Expertise.
We are a cryptographic company with the deepest expertise in cryptographic libraries.
Federal Focus.
In process for FedRAMP authorization.
Frictionless Deployment.
Market-leading integrations with products already in your infrastructure.
Partnering with Cybersecurity Juggernauts










Take Action Now
Discover. Remediate. Control. Let's connect to share how we can help you and your agency meet immediate requirements and continue you on your migration journey.



